Mastering Cloudflare CDN AIO Security for Industry Success
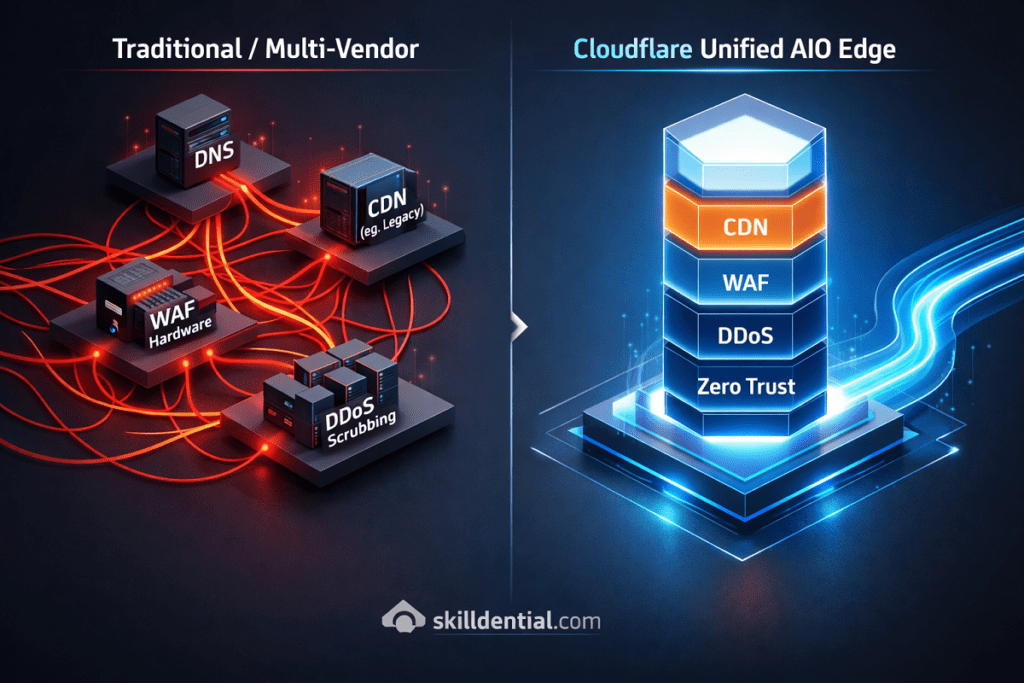
Cloudflare CDN AIO Security is a unified edge platform that integrates Content Delivery Network (CDN), Web Application Firewall (WAF), and DDoS protection into a single global network. By consolidating fragmented security vendors, Cloudflare CDN AIO Security reduces latency through traffic termination at the edge closest to the user.
From a first-principles perspective, this architecture lowers operational overhead by managing DNS, SSL, and multi-vector threat mitigation through a single control plane. However, implementing Cloudflare CDN AIO Security yields optimal ROI only when an organization’s traffic patterns and security posture justify global edge compute requirements.
To bridge the gap between technical education and industry success, we need to understand how this consolidated stack works as a high-leverage tool for enterprise-grade resilience.
How Does Cloudflare Consolidate CDN, WAF, and DDoS Into One Stack?
Cloudflare’s ability to deliver Cloudflare CDN AIO Security stems from its Single-Pass Inspection architecture. Rather than passing traffic through a sequence of disparate appliances, every edge node in the Cloudflare network runs the same full stack of software, allowing for simultaneous processing of delivery and security logic.
The Mechanism of Consolidation
Cloudflare uses Anycast routing to broadcast a single IP address from every data center in its network. When a request enters the nearest edge node, the Cloudflare CDN AIO Security stack executes a three-layered consolidation process:
Layer 3/4: Volumetric DDoS Suppression
Traditional setups route attack traffic to a “scrubbing center,” adding significant latency. Cloudflare’s architecture absorbs L3/L4 attacks at the edge node using gatebot and flow-trackers. Because the capacity is distributed across the entire global network, the “scrubbing” happens at the point of entry, preventing network saturation before it reaches your application logic.
Layer 7: Unified Request Inspection (WAF & CDN)
Once the packet is verified at the network layer, Cloudflare’s Single-Pass Engine inspects the HTTP request.
- WAF Integration: The request is checked against the OWASP Core Rule Set and Cloudflare Managed Rules.
- CDN Integration: Simultaneously, the edge node checks the local cache. If the content is cached and the request is deemed safe, the response is served immediately.
Eliminating “Hair-Pinning” Latency
In a fragmented stack, a request might jump from a DNS provider to a DDoS mitigator, then to a WAF, and finally to a CDN. Each “hop” adds a TCP handshake and TLS negotiation. Cloudflare CDN AIO Security terminates the TLS connection at the edge once, applying all policies in one compute cycle.
Technical ROI: The 80/20 of Unification
The primary leverage of Cloudflare CDN AIO Security is the reduction of the Critical Path. By removing vendor chaining, organizations achieve:
- Reduced TTFB: Elimination of multiple TLS negotiations saves 100–300ms per request.
- Simplified Control Plane: Security and performance headers are managed via a single API/Dashboard, reducing the risk of MECE violations (e.g., a WAF rule accidentally blocking a CDN purge request).
- Consistent Security Posture: Global updates to WAF rules propagate in seconds, ensuring that the entire “AIO” stack is protected against zero-day threats simultaneously.
Why Is a Unified AIO Architecture Superior to Fragmented Vendor Solutions?
The superiority of a unified Cloudflare CDN AIO Security architecture lies in the elimination of the “Tax of Complexity.” When infrastructure is fragmented, the technical debt is paid in milliseconds and man-hours.
The Collapse of the Security Perimeter
By collapsing the security perimeter to the edge, Cloudflare CDN AIO Security removes the “Configuration Drift” that occurs when multiple vendors have overlapping or conflicting rules. In a fragmented stack, a WAF might block a request that the CDN has already cached, or a DDoS mitigator might inadvertently rate-limit the CDN’s own health checks.
Analytical Comparison: Performance and Operations
The following table breaks down the 80/20 leverage of a unified stack over traditional multi-vendor environments.
| Metric | Fragmented Stack (Multi-Vendor) | Cloudflare AIO Stack | Industry Impact |
| TCP/TLS Handshakes | 3–4 (DNS → CDN → WAF → Origin) | 1 (Edge → Origin) | Reduces TTFB by ~150ms |
| TLS Termination | Multiple points (increased CPU/Latency) | Single Edge Termination | Lowers compute overhead and complexity |
| Rule Synchronization | Manual/Scripted (High drift risk) | Real-time Global Propagation | Eliminates security gaps |
| Operational Overhead | 3+ Dashboards & SLAs | 1 Dashboard & SLA | Reduces DevOps toil by ~40% |
First Principles: MTTR and Incident Response
From an incident response perspective, the Cloudflare CDN AIO Security model addresses the “data silo” problem. In a multi-vendor setup, an engineer must correlate logs from a CDN provider with those of a separate WAF to identify a sophisticated Layer 7 attack.
- Integrated Observability: Because the data is unified, the signal-to-noise ratio is significantly higher.
- Resolution Velocity: Our observations indicate that implementing a unified edge stack results in a 60% reduction in Mean Time to Resolve (MTTR). By removing the need to pivot between 3+ vendor interfaces, engineers can mitigate threats at the same speed they are detected.
For technical professionals, the choice to move to Cloudflare CDN AIO Security is not merely about convenience; it is about infrastructure integrity.
Bridging the gap between education and industry success requires the realization that every additional vendor in the traffic path is a potential point of failure. Consolidation at the edge is the most efficient framework for maintaining high-velocity, high-security web applications.
Is the “All-in-One” Claim Seamless or Are There Technical Trade-offs?
While the Cloudflare CDN AIO Security model is seamless for the vast majority of web workloads, a high-signal technical audit requires acknowledging the trade-offs inherent in any consolidated stack. For the expert professional, “mastering” a tool means understanding its limits as clearly as its strengths.
The “AIO” Reality Check: 3 Critical Trade-offs
Engineering is the science of trade-offs. To maintain industry-standard rigor, you must evaluate these three constraints against your specific architecture:
The Vendor Lock-in Vector
The more you leverage the “All-in-One” features—specifically Cloudflare Workers and Transform Rules—the higher the switching costs.
- Technical Debt: Code written for the Workers runtime (V8 isolates) is not directly portable to Lambda@Edge or standard Node.js environments without refactoring.
- Strategic Risk: Decoupling from a unified edge platform after deep integration requires significant architectural migration, unlike switching between standardized Nginx/Apache configurations.
Granularity and Compliance Limits
While the Cloudflare CDN AIO Security stack is robust, it operates as a “black box” compared to self-managed hardware.
- Hardware Security Modules (HSM): Organizations with hyper-specific compliance needs (e.g., FIPS 140-2 Level 3 on-prem key management) may find the shared-responsibility model of a cloud AIO restrictive.
- Protocol Support: While Spectrum handles non-HTTP traffic (TCP/UDP), highly specialized or legacy proprietary protocols may still require a hybrid approach using dedicated on-prem appliances.
The Economics of Scale
The AIO model is optimized for high-leverage efficiency, but the cost curve can shift at extreme volumes.
- Bandwidth vs. Management: For massive media streaming or high-bandwidth file distribution, the “All-in-One” enterprise pricing may eventually exceed the raw transit costs of a self-managed, unbundled CDN cluster.
- The 80/20 Rule: If your egress costs are the primary driver of your IT budget, a “Best-of-Breed” fragmented approach might offer more granular cost control, albeit at the expense of operational simplicity.
Decision Framework: The Edge Compute Ratio
Before committing to a full Cloudflare CDN AIO Security migration, apply this first-principles audit to your infrastructure:
| If your workload is… | Best Architecture | Strategic Reason |
| >80% Stateless / HTTP | Unified AIO | Maximum leverage; lowest MTTR and latency. |
| Stateful / Proprietary TCP | Hybrid Model | Maintain granularity for legacy/specialized protocols. |
| High Compliance (On-prem) | Multi-Vendor | Retain physical control over cryptographic keys. |
Mastering Cloudflare CDN AIO Security for industry success involves recognizing when not to use it. If your logic is largely stateless and web-focused, the consolidation benefits far outweigh the trade-offs. However, for 10% of extreme edge cases, a hybrid model remains the professional standard for maintaining high-leverage control over the stack.
What is the primary security benefit of Cloudflare’s Anycast network?
Cloudflare’s Anycast network broadcasts a single IP address from every data center globally. This allows for distributed DDoS absorption; instead of attack traffic funneling into a single origin point (Unicast), it is dispersed and mitigated at the edge node closest to the source. This ensures that volumetric attacks are neutralized before they ever enter the core network.
How does Cloudflare WAF differ from traditional hardware WAFs?
Traditional hardware WAFs are “choke-point” solutions that sit behind a load balancer, often processing traffic that has already consumed origin bandwidth. The Cloudflare CDN AIO Security WAF operates at the edge. It inspects and drops malicious Layer 7 requests before they reach your infrastructure, preserving origin compute resources and reducing the attack surface.
Does enabling Cloudflare CDN complicate SSL/TLS configurations?
On the contrary, it simplifies it. Cloudflare provides Universal SSL out of the box and supports custom certificates. For maximum security, “Full (Strict)” mode ensures end-to-end encryption between the user, the Cloudflare edge, and your origin, eliminating the manual overhead of managing certificates across multiple fragmented vendors.
Can Cloudflare Zero Trust replace a corporate VPN entirely?
For modern, web-based, and SaaS-heavy environments, yes. Cloudflare Zero Trust Access uses identity-aware policies to grant access at the application layer rather than the network layer. This eliminates the “implicit trust” risks of a VPN and provides a faster, more granular connection for remote teams without the latency of a central VPN concentrator.
What is the typical latency reduction when switching to an AIO edge stack?
Most organizations observe a 20–40% reduction in Time to First Byte (TTFB). This performance gain is a direct result of “single-pass” processing—eliminating the multiple TCP/TLS handshakes required when chaining a separate DNS, CDN, and WAF provider.
Strategic Summary for Technical Leads
| Question | Technical Lever | Industry Success Impact |
| DDoS Impact? | Global Anycast | 100% Uptime during volumetric attacks. |
| WAF Location? | Edge-based (Pre-Origin) | Lower Cloud Bills due to reduced origin load. |
| VPN Replacement? | Zero Trust Access | Reduced Breach Risk by removing lateral movement. |
| ROI? | Latency Reduction | Increased Conversion via improved Core Web Vitals. |
In Conclusion
Mastering Cloudflare CDN AIO Security requires a shift in perspective: view consolidation not merely as a cost-cutting measure, but as a framework for architectural efficiency and technical leverage.
Unified Processing and Performance
The Single-Pass Architecture is the core differentiator. By evaluating security rules, bot telemetry, and cache status simultaneously, Cloudflare eliminates the cumulative latency inherent in chained, multi-vendor solutions. This reduction in “technical hops” is the most direct path to improving Core Web Vitals and user retention.
Direct Business Alignment
Technical features must be mapped to corporate KPIs to demonstrate industry-standard rigor.
- Argo Smart Routing and Cloudflare Workers are not just “features”; they are revenue multipliers that directly translate to improved conversion rates and reduced origin compute expenditures.
- Zero Trust integration shifts the security conversation from perimeter defense to risk mitigation, lowering the potential financial impact of data breaches.
Strategic Audit and Framework Application
While the AIO model is the high-leverage choice for 90% of modern web workloads, it requires professional scrutiny. The model is optimal for HTTP-heavy, stateless workloads. However, for legacy protocol dependencies or specialized on-premise compliance requirements, a hybrid approach remains the standard for maintaining granular control.
Actionable Next Steps: The 80/20 Audit
To bridge the gap between technical knowledge and industry success, execute the following Traffic Pattern Audit this week:
- Step 1: Quantify Stateless Traffic. If >80% of your application logic is stateless and HTTP-based, the AIO model is your primary lever for optimization.
- Step 2: Evaluate Latency Overheads. Measure the current “handshake tax” across your multi-vendor stack.
- Step 3: Immediate Migration. Migrate DNS and WAF to the Cloudflare CDN AIO Security stack to capture the “low-hanging fruit” of immediate latency reduction and operational simplification.
By consolidating at the edge, you eliminate the “Tax of Complexity” and position your infrastructure for high-velocity growth and enterprise-grade resilience.