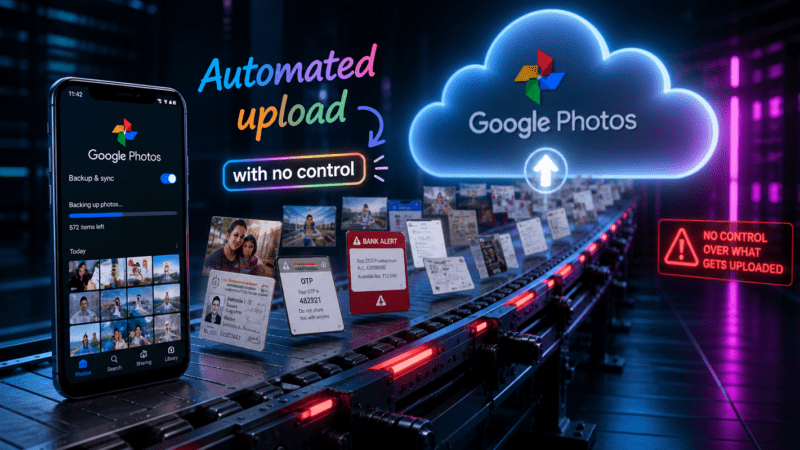
Google Photos Backup Security uses AES-256 encryption for data at rest and in transit across Google’s global infrastructure. This industry-standard protocol ensures that intercepted data remains unreadable to unauthorized external parties. However, a key technical
Tag: Cloud Computing
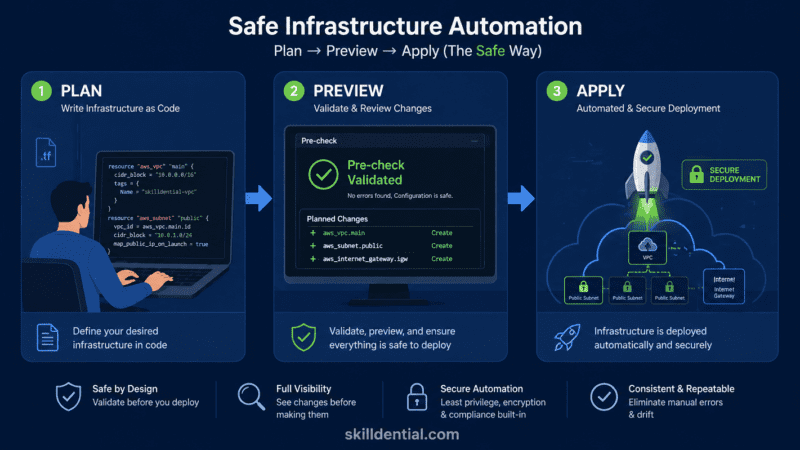
The implementation of IaC tools in DevOps represents a fundamental shift from manual hardware configuration to a software-defined ecosystem. By treating infrastructure as version-controlled code, organizations can achieve high-leverage scalability while maintaining rigorous safety standards.
The best website hosting service for scalable web traffic is defined by managed cloud or VPS architectures capable of autonomous resource scaling, 99.99% uptime, and global CDN integration. Achieving sub-second latency during traffic spikes is
Cloudflare Reverse Proxy functions as a high-leverage abstraction layer between client requests and backend origin servers. By decrypting and re-encrypting HTTPS traffic at the network edge, it offloads critical security and optimization tasks that would
A Cloudflare outage refers to a disruption in internet services caused by failures within Cloudflare’s global content delivery and security infrastructure. Between late 2025 and early 2026, the network experienced a series of high-profile “Code
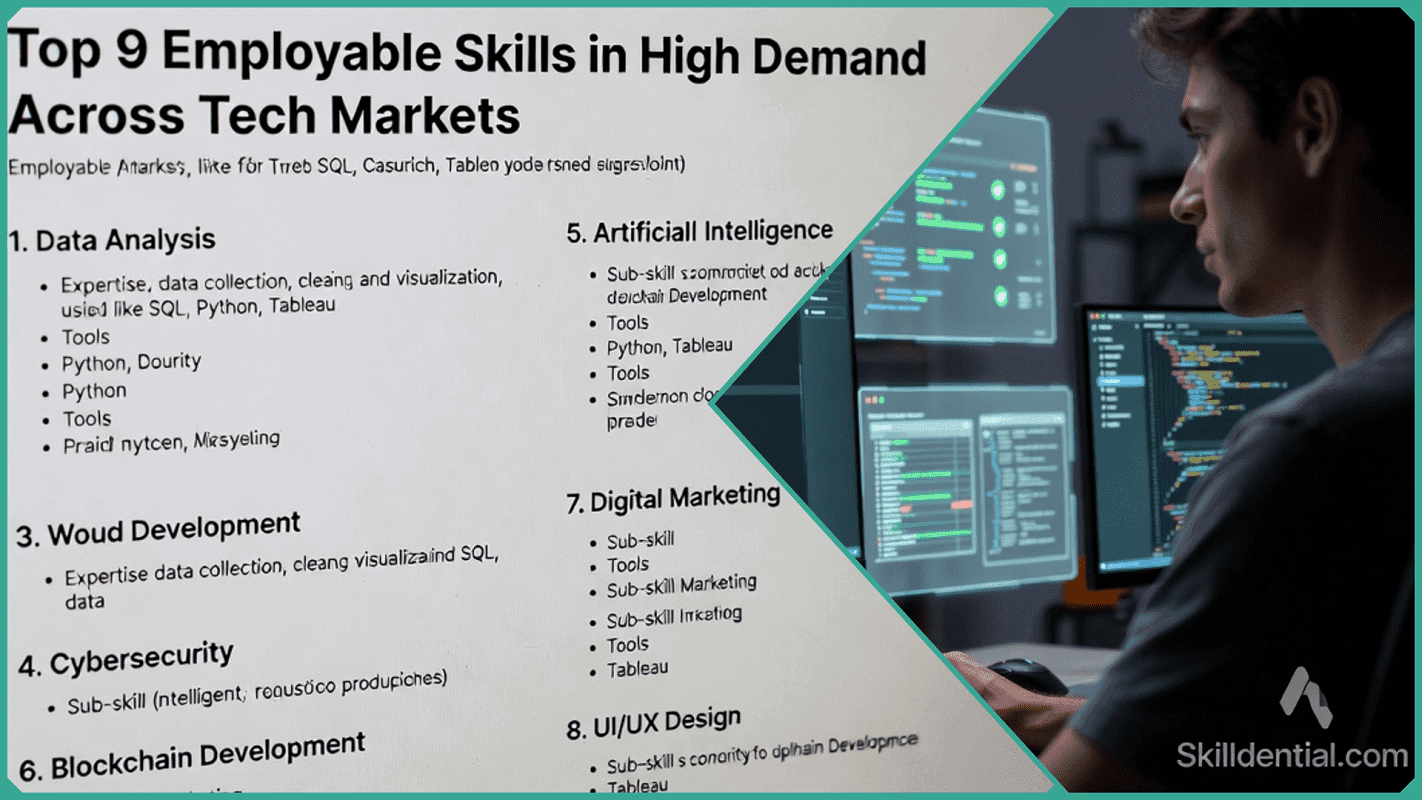
What exactly defines an employable skill in 2026? Simply put, it is a practical competency that directly impacts your job performance and makes you a “must-hire” in the eyes of recruiters. As tech integration accelerates,