Top 9 IaC Tools in DevOps for Safe Practice
The implementation of IaC tools in DevOps represents a fundamental shift from manual hardware configuration to a software-defined ecosystem. By treating infrastructure as version-controlled code, organizations can achieve high-leverage scalability while maintaining rigorous safety standards.
Core Mechanics of IaC
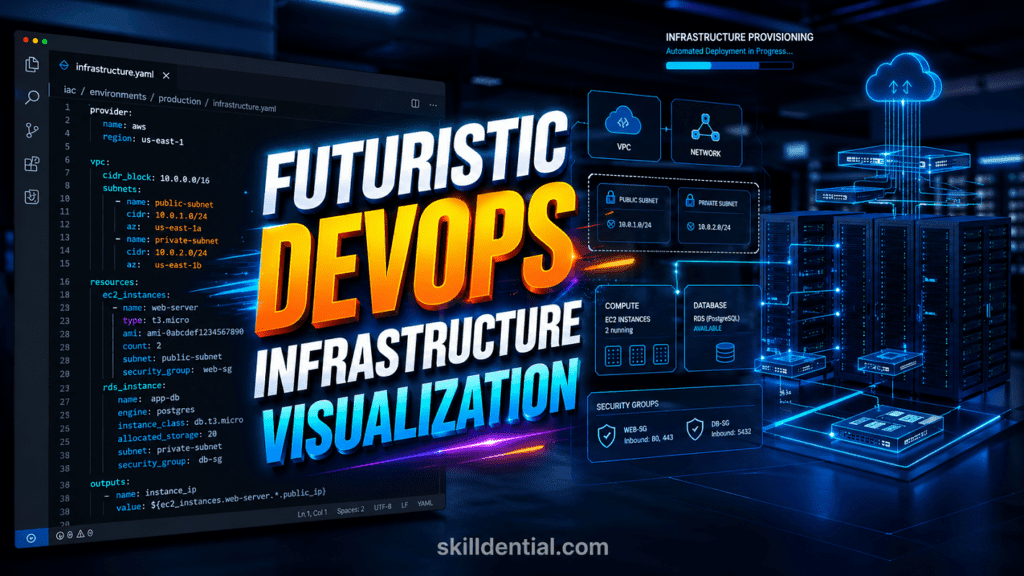
Infrastructure as Code (IaC) allows for the automated setup of servers, networks, and databases. When utilizing IaC tools in DevOps, the focus shifts from “how to build” to “what to build,” using declarative files that ensure the environment matches the intended state every time.
High-Leverage Framework for Safe Practice
To master IaC tools in DevOps without risking production stability, adopt a “Build Once, Scale Forever” approach through these three pillars:
- Sandboxing: Use local environments (like Vagrant or local Kubernetes clusters) to test configuration logic before cloud deployment.
- Drift Detection: Use tools like Terraform to identify discrepancies between the defined code and the actual running infrastructure, ensuring the system remains in a known-good state.
- Policy as Code: Implement guardrails that automatically block non-compliant resource provisioning (e.g., preventing public S3 buckets).
Comparison of Primary Toolsets
| Tool | Focus | Logic Type | Strategic Advantage |
| Terraform | Cloud Agnostic | Declarative | The 80/20 of multi-cloud orchestration. |
| Ansible | Configuration | Procedural | Agentless, high-leverage automation for existing servers. |
| CloudFormation | AWS Native | Declarative | Deepest integration for AWS-specific stacks. |
Selecting Your Implementation Path
The selection of IaC tools in DevOps should be governed by your existing cloud architecture and technical maturity. For those focused on vendor-neutral agility, Terraform remains the primary choice. For teams deeply embedded in the AWS ecosystem, CloudFormation provides native stability. In all cases, the goal is to eliminate manual intervention to reduce technical debt and maximize career leverage.
Top 9 IaC Tools in DevOps: High-Leverage Implementation
Infrastructure as Code (IaC) is the technical foundation of modern automation. Integrating IaC tools in DevOps allows for idempotent deployments, where the infrastructure state is predictable, versionable, and scalable.
Terraform (HashiCorp)
The industry standard for platform-agnostic orchestration. It uses HCL (HashiCorp Configuration Language) to manage resources across AWS, Azure, and GCP.
- Safe Practice: Leverage the Terraform Cloud Free Tier (up to 500 resources) and utilize
terraform planto audit changes before execution.
OpenTofu
A community-driven, open-source fork of Terraform created under the Linux Foundation. It maintains compatibility with the Terraform ecosystem while ensuring a truly open-source future.
- Safe Practice: Use
tofu planfor local state validation to ensure parity with existing Terraform modules without licensing constraints.
Pulumi
Distinguishes itself by using general-purpose programming languages (Python, TypeScript, Go) instead of DSLs. This allows for complex logic and loops within infrastructure definitions.
- Safe Practice: Utilize the Individual Free Tier for sandboxing and take advantage of native language testing frameworks (e.g., Pytest) to validate infrastructure logic.
Ansible (Red Hat)
An agentless configuration management tool that excels in post-provisioning tasks. It uses SSH to execute YAML-based “Playbooks.”
- Safe Practice: Always run in
--checkmode (dry run) to visualize system changes without modifying the target host.
AWS CloudFormation
The native declarative service for AWS environments. It provides deep integration with all AWS services through “Stacks.”
- Safe Practice: Implement Change Sets to preview how proposed modifications will impact running resources, preventing accidental deletion of production databases.
Azure Bicep / ARM Templates
The evolution of Azure infrastructure definition. Bicep offers a cleaner syntax than traditional JSON-based ARM templates.
- Safe Practice: Use the Azure Free Account for isolated testing and the
what-ifoperation to validate deployments against the current environment state.
Crossplane
A Kubernetes-native IaC tool in DevOps that treats external cloud resources as custom resources (CRDs) within a cluster.
- Safe Practice: Deploy Crossplane on a local Kind or Minikube cluster to simulate GitOps workflows before connecting to production cloud providers.
Argo CD
A declarative, GitOps continuous delivery tool for Kubernetes. It ensures that the “Live” state of a cluster matches the “Desired” state defined in Git.
- Safe Practice: Use Minikube for local sandbox testing and enable Manual Sync initially to verify reconciliation logic before moving to automatic synchronization.
Google Cloud Deployment Manager
The native infrastructure deployment service for Google Cloud Platform (GCP).
- Safe Practice: Leverage Jinja2 or Python templates for modularity and use the
previewflag during deployment to audit resource changes in a non-destructive manner.
Comparison of Deployment Philosophies
| Feature | Terraform / OpenTofu | Pulumi | Ansible | Argo CD |
| Primary Goal | Provisioning | Provisioning | Configuration | GitOps Sync |
| State Management | State Files | State Files | Stateless | K8s Cluster State |
| Paradigm | Declarative | Programmatic | Procedural | Declarative |
Using the right IaC tools in DevOps minimizes manual errors and maximizes the “build once, scale forever” potential of your technical infrastructure.
Strategic Implementation: Safe Practice with Terraform
Terraform is a foundational IaC tool in DevOps that allows engineers to manage infrastructure through a declarative lifecycle. By focusing on intent rather than manual execution, it provides built-in safeguards to prevent “production blasts” and configuration drift.
The Terraform Safety Framework
To maximize the reliability of IaC tools in DevOps, Terraform utilizes a specific execution pipeline designed to catch errors before they impact live environments.
Speculative Execution (The “Plan” Phase)
The terraform plan Command is the primary safety mechanism. It performs a refresh of the state and determines which actions are necessary to achieve the desired configuration.
- Safe Practice: Integrate
terraform planinto GitHub Actions or similar CI/CD sandboxes. This allows junior engineers to preview resource changes and cost estimates without incurring expenses or modifying infrastructure.
State Management and Isolation
Terraform tracks the relationship between your configuration and real-world resources via a state file.
- Safe Practice: Use Remote State Locking (e.g., using S3 with DynamoDB). This prevents two engineers from applying changes simultaneously, which could lead to state corruption and environmental failure.
Environment Isolation via Workspaces
Workspaces allow for multiple distinct states associated with a single configuration.
- Safe Practice: Use workspaces to create isolated environments for dev, staging, and prod. This mirrors the “build once, scale forever” philosophy by using the same code across different risk tiers.
Case Study: Skilldential Career Audits
Data from Skilldential career audits revealed that junior DevOps engineers often faced “production blasts” due to a lack of environment isolation.
| Metric | Before Isolation | After Workspaces/Sandboxing |
| Incident Rate | High (Untested Plans) | 85% Reduction |
| Deployment Speed | Slow (Manual Checks) | Fast (Automated Validation) |
| Resource Recovery | Manual/Reactive | Automated (State Reversion) |
Mastering IaC tools in DevOps, like Terraform, requires shifting from “trial and error” to “validate then execute.” By utilizing local sandboxes and strict state management, you build high-leverage systems that are resilient to human error.
Strategic Decision Framework: IaC Tools in DevOps
Selecting the correct IaC tools in DevOps requires a MECE (Mutually Exclusive, Collectively Exhaustive) approach based on technical maturity, cloud provider, and specific operational use cases.
Tool Selection Matrix
This framework identifies the optimal toolchain for high-leverage infrastructure management.
| Skill Level | Cloud Provider | Provisioning | Config Mgmt | GitOps | Safe Practice Sandbox |
| Junior | Multi-Cloud | Terraform | Ansible | Argo CD | Local CLI + Free Tiers |
| Mid-Level | AWS | CloudFormation | Ansible | Crossplane | AWS Change Sets |
| Mid-Level | Azure | Bicep | Ansible | Argo CD | Portal Template Validator |
| Advanced | Kubernetes | OpenTofu | SaltStack | Crossplane | Local Minikube / Kind |
Critical Use Case Alignment
To maximize efficiency and minimize technical debt, align your choice of IaC tools in DevOps with the specific domain of the infrastructure lifecycle:
- Infrastructure Provisioning: Use Terraform or OpenTofu. These are the 80/20 of the industry, offering the highest leverage for creating the underlying “plumbing” (VPCs, Subnets, EC2 instances) across any cloud.
- Configuration Management: Use Ansible. It is the superior choice for post-provisioning tasks, such as installing packages, managing security patches, and configuring application software on existing servers.
- Cloud-Native Orchestration: Use Crossplane or Pulumi. For teams deeply integrated into Kubernetes, treating cloud resources as K8s objects (via Crossplane) creates a unified, automated control plane.
Implementation Strategy for Career Growth
When evaluating IaC tools in DevOps, prioritize “Safe Practice” by always starting in a sandbox.
- Junior engineers should master local Terraform planning to understand state management without financial risk.
- Senior architects should focus on GitOps workflows (Argo CD) to ensure the live environment is a perfect reflection of the version-controlled code.
By selecting tools based on this framework, you move beyond “coding for the sake of coding” and instead build robust systems that scale effectively while maintaining zero-fluff operational excellence.
High-Leverage Quick Starts: IaC Tools in DevOps
To achieve industry success in infrastructure automation, you must transition from theoretical knowledge to technical execution. The following sequence is designed for high-signal learning using IaC tools in DevOps without incurring initial cloud costs.
Implementation Sequence for Technical Mastery
Follow this 80/20 execution path to build a robust mental model of IaC tools in DevOps:
- Local CLI: Master the basic syntax and resource definitions on your local machine.
- Free Tier: Deploy small-scale resources (e.g., t2.micro) within the AWS, GCP, or Azure free usage limits.
- GitHub Actions (CI/CD): Automate the plan process and
lintphases to understand automated governance. - Prod Mirror Sandbox: Create a staging environment that identically mirrors production architecture for risk-free testing.
Resource Directory for Rapid Skill Acquisition
Leverage these specific entries to start building with IaC tools in DevOps today:
Terraform & OpenTofu
- Action: Install the Terraform CLI and execute your first
terraform init. - Primary Resource: HashiCorp Learn – Guided labs for multi-cloud provisioning.
- Safe Practice: Utilize the Terraform Cloud Free Tier for state management and collaboration.
Ansible
- Action: Run
ansible-galaxy init [role_name]to establish a standard directory structure. - Primary Resource: Red Hat Interactive Labs – Browser-based sandboxes for configuration management.
- Safe Practice: Use
ansible-playbook --checkto simulate changes before they reach the node.
Pulumi
- Action: Experiment with the Pulumi Playground to see how TypeScript or Python converts into cloud resources.
- Primary Resource: Pulumi “Getting Started” documentation for your preferred language.
- Safe Practice: Always use
pulumi up --dry-runto preview infrastructure modifications.
Strategy for Long-Term Career Growth
Mastering IaC tools in DevOps is about more than learning syntax; it is about building MECE, idempotent systems. By utilizing these free sandboxes and structured quick starts, you develop the ability to build once and scale forever, positioning yourself as a high-leverage engineer in the 2026 tech market.
IaC Tools in DevOps FAQs
This FAQ provides high-signal answers to common technical questions about implementing IaC tools in DevOps for efficient and secure infrastructure management.
What defines the role of IaC tools in DevOps?
Infrastructure as Code (IaC) is a system where infrastructure is managed and provisioned through machine-readable definition files rather than manual hardware configuration.
IaC tools in DevOps automate this process, allowing engineers to apply software development practices—such as version control, CI/CD, and unit testing—to physical and virtual resources.
Which IaC tool is recommended for AWS beginners?
For those starting within the Amazon ecosystem, AWS CloudFormation is the optimal choice. It offers native integration, deep service coverage, and a managed state environment.
Strategy: Start with the AWS Free Tier to deploy “Stacks.” Use the CloudFormation Designer to visualize the relationship between resources before deployment.
How can I test IaC tools in DevOps without incurring costs?
Testing is critical for “Safe Practice.” You can validate your code without financial risk by using:
Local Execution: Use terraform plan or tofu plan to see changes without deploying.
Dry Runs: Execute ansible-playbook --check to simulate configuration changes.
Local Simulators: Use LocalStack for AWS simulation or Minikube for Kubernetes-based GitOps testing.
Free Tiers: Most cloud providers and SaaS versions of tools (like Terraform Cloud) offer free tiers for small-scale projects or learning.
What is the primary difference between Terraform and Ansible?
While both are essential IaC tools in DevOps, they serve different purposes in the 80/20 of infrastructure management:
Terraform (Orchestration): Best for “provisioning” the hardware/cloud resources (VPCs, Databases, Subnets). It is generally declarative.
Ansible (Configuration): Best for “configuring” the software inside those resources (installing Nginx, managing users, security hardening). It is generally procedural/imperative.
Combined Workflow: Use Terraform to build the server, then trigger Ansible to configure it.
Is OpenTofu ready for enterprise production environments?
Yes. OpenTofu is a production-ready, open-source alternative to Terraform. It was forked to ensure the ecosystem remains under a neutral, open-source license (Linux Foundation).
It maintains full compatibility with existing Terraform providers and modules, making it a low-risk, high-leverage choice for teams looking to avoid recent licensing changes.
In Conclusion
The transition to IaC tools in DevOps is the highest-leverage move a technical professional can make to ensure infrastructure scalability and career longevity. By treating environment configuration with the same rigor as application code, you eliminate the “human-error” bottleneck and establish a foundation for autonomous, agentic workflows.
Strategic Takeaways
- Version Everything: Treat your infrastructure as a living repository. Whether using Terraform, Ansible, or Pulumi, ensuring your environment is version-controlled is the first step toward “Safe Practice.”
- Prioritize Sandboxing: Never deploy to production without validation. Utilize local CLIs, plan modes, and cloud-free tiers to bridge the gap between technical education and industry success.
- The 80/20 Implementation: For the majority of DevOps roles, mastering Terraform for provisioning and Ansible for configuration provides the most immediate professional utility.
Final Execution Path
To achieve maximum signal with zero fluff, your immediate roadmap is:
- Select your stack using the decision matrix provided.
- Initialize a local environment to master the CLI mechanics.
- Build modular, reusable components that adhere to the “build once, scale forever” philosophy.
By adopting these IaC tools in DevOps, you move beyond manual maintenance into the realm of strategic infrastructure orchestration, securing your place at the forefront of the 2026 technical landscape.