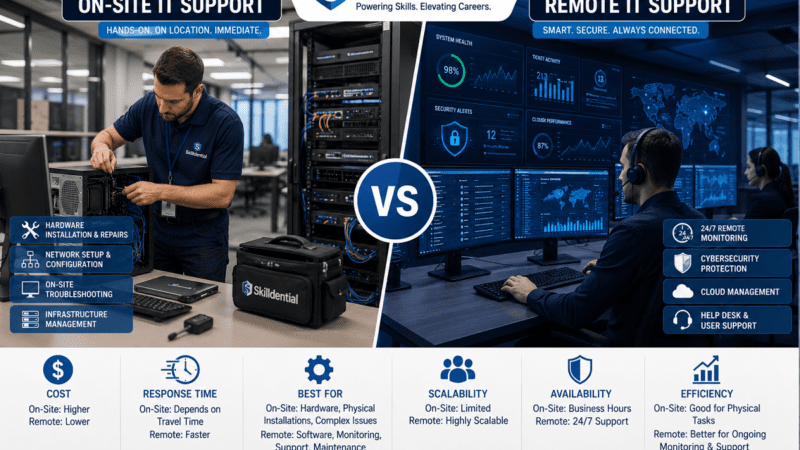
Remote IT support for small businesses functions as a scalable operational framework, providing outsourced technical management via secure internet-based protocols. By centralizing oversight of networks and endpoints, organizations replace the overhead of full-time on-site personnel
Tag: Cybersecurity
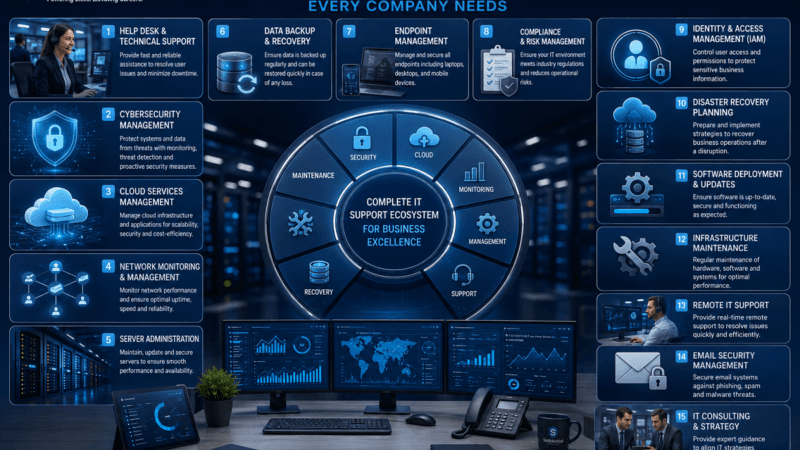
In an era where technology dictates operational capacity, Business IT Support Services serve as the backbone of sustainable growth. These services encompass the technical, operational, and security functions necessary to maintain a reliable infrastructure, protect
In an era where hybrid operations are the standard, the perimeter of the corporate network has effectively dissolved. Remote work security best practices are no longer optional guidelines; they are the fundamental architecture protecting company
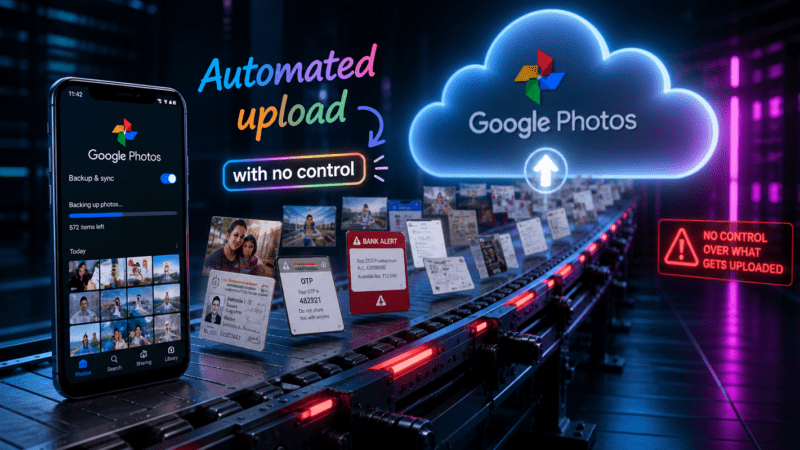
Google Photos Backup Security uses AES-256 encryption for data at rest and in transit across Google’s global infrastructure. This industry-standard protocol ensures that intercepted data remains unreadable to unauthorized external parties. However, a key technical
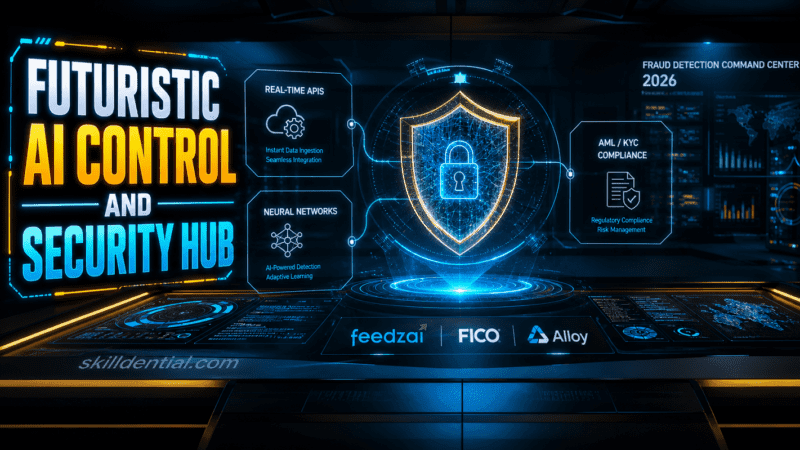
Financial fraud detection software has evolved from a defensive cost center into a strategic growth lever for modern fintechs. By leveraging real-time telemetry and advanced machine learning models, this software analyzes high-velocity transaction streams and
Landing your first cybersecurity job in Nigeria requires mastering the 20% of high-leverage skills—such as cloud security, AI-driven threat detection, and SOC analysis—that drive 80% of hiring outcomes. As of early 2026, demand for specialized
Okta Zero Trust implements NIST 800-207 by mapping the Okta Identity Provider (IdP) to the Policy Decision Point (PDP) and its distributed agents or gateways to Policy Enforcement Points (PEP). This architecture ensures that every
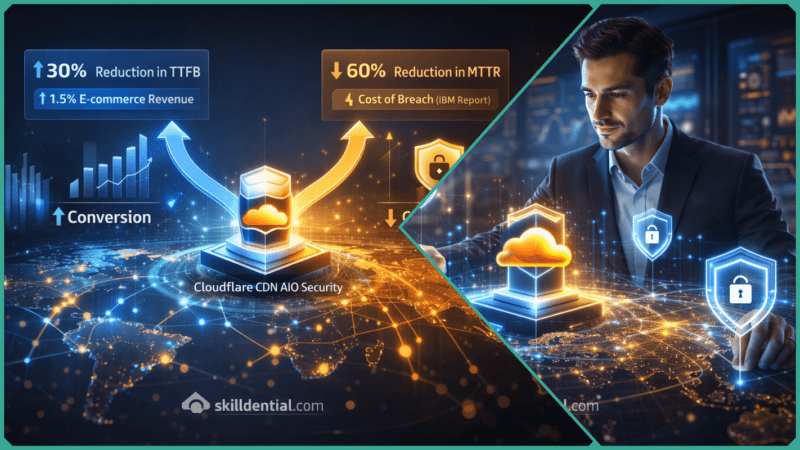
Cloudflare CDN AIO Security is a unified edge platform that integrates Content Delivery Network (CDN), Web Application Firewall (WAF), and DDoS protection into a single global network. By consolidating fragmented security vendors, Cloudflare CDN AIO
In 2026, the Nigerian labor market exhibits a sharp divergence between traditional academic output and industry-standard requirements. High-paying tech skills represent the critical 20% of competencies—specifically AI engineering, cloud orchestration, and cybersecurity—that generate 80% of
Cloudflare Reverse Proxy functions as a high-leverage abstraction layer between client requests and backend origin servers. By decrypting and re-encrypting HTTPS traffic at the network edge, it offloads critical security and optimization tasks that would
A Cloudflare outage refers to a disruption in internet services caused by failures within Cloudflare’s global content delivery and security infrastructure. Between late 2025 and early 2026, the network experienced a series of high-profile “Code
A financial fraud lawyer provides specialized litigation and recovery strategies for victims of investment scams, wire fraud, and sophisticated embezzlement. In an era where AI-driven deceit—such as synthetic identity theft and deepfake-authorized transfers—bypasses traditional security,